Building a Cybersecurity Program That Actually Holds
From Zero to Resilient
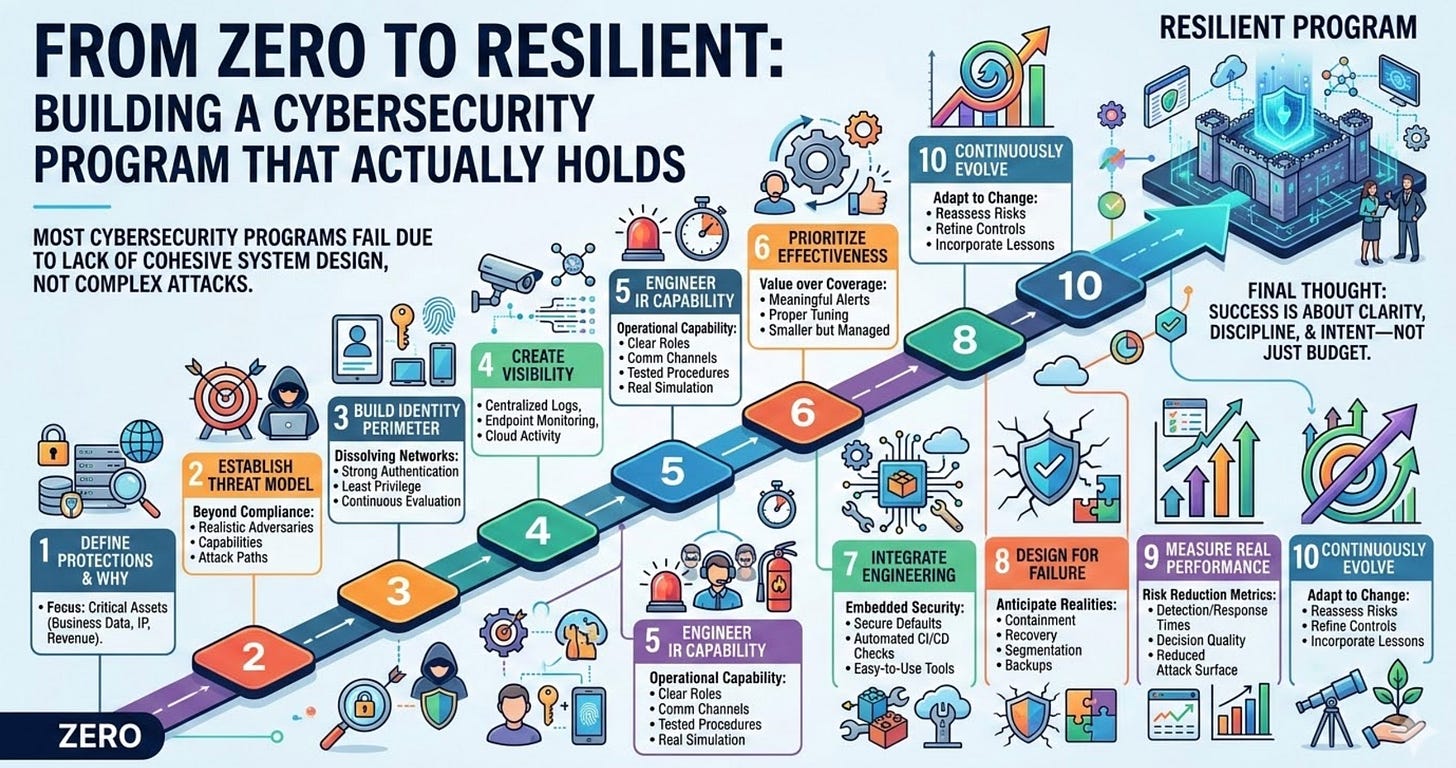
Most cybersecurity programs do not fail because of sophisticated attackers or novel zero-day exploits. They fail because they were never engineered to function as cohesive systems in the first place.
Many programs begin as compliance-driven checklists, evolve into fragmented collections of tools, and eventually become too complex to operate effectively. Over time, this complexity creates blind spots, slows response times, and erodes confidence across the organization.
If you are building a cybersecurity program from the ground up, or attempting to rebuild one that exists only in policy documents, your task is not simply to deploy controls. You are designing a system that must enable consistent, high-quality decision-making under pressure.
The following steps represent the foundational elements of a program that is built to endure.
1. Define What You Are Protecting and Why
Before selecting tools or implementing frameworks, it is essential to understand what truly matters to the organization. This requires identifying the assets that are critical to business operations and long-term success.
These assets often include customer data, intellectual property, revenue-generating systems, and operational infrastructure. However, the importance of each asset depends on the specific context of the business.
Organizations that skip this step often misallocate resources by overprotecting low-value systems while leaving critical assets exposed. A well-designed program begins with a clear alignment between security priorities and business objectives.
2. Establish a Threat Model Rather Than Relying Solely on Compliance
Compliance frameworks provide useful guidance, but they are inherently generalized and do not reflect the specific risks faced by your organization.
A threat model forces you to consider who might realistically target your organization, what capabilities those adversaries possess, and which attack paths they are most likely to exploit. This process transforms security from a theoretical exercise into a practical, context-driven discipline.
Without a threat model, organizations tend to spread their defenses too thin, attempting to protect against every possible risk rather than focusing on the most probable and impactful threats.
3. Build Identity as the Primary Security Perimeter
In modern environments, the traditional network perimeter has largely dissolved. Users, devices, and services operate across cloud platforms, remote networks, and third-party integrations.
As a result, identity has become the central control point for security. A strong program prioritizes robust authentication mechanisms, enforces least privilege access, and continuously evaluates user behavior.
If identity controls are weak or inconsistently applied, attackers can bypass other defenses with relative ease. Establishing a strong identity foundation ensures that all subsequent security layers are built on stable ground.
4. Create Visibility Before Attempting to Enforce Control
Effective security depends on accurate and comprehensive visibility into system activity. Without this visibility, it is impossible to detect anomalies, investigate incidents, or validate the effectiveness of controls.
Organizations should prioritize centralized logging, endpoint monitoring, network telemetry, and cloud activity tracking. These capabilities provide the data necessary to understand what is happening across the environment.
Deploying controls without first establishing visibility often leads to false confidence, as teams lack the evidence required to confirm whether those controls are functioning as intended.
5. Engineer a Practical Incident Response Capability
An incident response plan documented in a policy is not sufficient. What organizations need is an operational capability that can function effectively during a crisis.
This capability includes clearly defined roles and responsibilities, established communication channels involving legal and public relations teams, and tested procedures for handling common incident scenarios.
Regular exercises should simulate realistic conditions, including incomplete information and time pressure. This ensures that leadership and technical teams are prepared to make informed decisions when it matters most.
6. Prioritize Control Effectiveness Over Control Coverage
The effectiveness of a cybersecurity program is not determined by the number of tools deployed or controls implemented. It is determined by how well those controls perform in practice.
Organizations should evaluate whether their controls are functioning as expected, whether alerts are meaningful and actionable, and whether response processes are efficient.
A smaller set of well-maintained and properly tuned controls will consistently outperform a large, unmanaged collection of tools that generate noise without delivering value.
7. Integrate Security Into Engineering Workflows
Security mechanisms that operate independently of engineering processes are often bypassed, either intentionally or unintentionally.
To be effective, security must be embedded into the development lifecycle. This includes implementing secure defaults, integrating automated checks into CI/CD pipelines, and providing developers with tools that are both effective and easy to use.
By aligning security with engineering workflows, organizations can ensure that secure practices are consistently applied without creating unnecessary friction.
8. Design for Failure Rather Than Assuming Perfection
No security program can prevent every incident. Systems fail, controls degrade, and attackers adapt.
A resilient program anticipates these realities by focusing on containment, recovery, and continuity. This includes implementing network segmentation to limit the spread of attacks, maintaining reliable backup systems, and establishing clear processes for restoring operations.
By planning for failure, organizations reduce the potential impact of incidents and improve their ability to recover quickly.
9. Measure Outcomes That Reflect Real Security Performance
Metrics should provide insight into how effectively the program is reducing risk and responding to threats.
Instead of focusing on superficial indicators such as the number of alerts generated or tools deployed, organizations should measure detection and response times, the speed and quality of decision-making during incidents, and the overall reduction in attack surface.
These metrics offer a more accurate view of the program’s maturity and effectiveness.
10. Continuously Evolve the Program
Threat actors continuously adapt their techniques, developing new methods to bypass defenses and exploit emerging technologies. As a result, the threat landscape is in a constant state of change.
At the same time, the organization’s technology environment evolves as new systems are introduced, legacy systems are retired, and architectures shift toward cloud and distributed models. These changes create new dependencies and potential vulnerabilities.
Additionally, the business itself changes over time, whether through growth, new product lines, acquisitions, or shifts in strategy. Each of these changes alters the organization’s risk profile.
A cybersecurity program must evolve in response to all of these factors. This requires regular reassessment of risks, continuous refinement of controls, and the incorporation of lessons learned from past incidents and near misses.
Final Thought
Building a cybersecurity program is not simply a technical exercise. It is the process of creating a system that enables the organization to operate with confidence in the face of uncertainty.
When a significant incident occurs, tools and technologies will play an important role. However, the effectiveness of the response will ultimately depend on the quality of the decisions made and the strength of the underlying program design.
Organizations that succeed in this effort are not necessarily those with the largest budgets, but those that approach cybersecurity with clarity, discipline, and intent.